Join the conversation:
#summitbuzz23
When
Thursday, June 8, 2023
7:30 am - 1:30 pm
Where
MassBay Community College
50 Oakland Street
Wellesley, MA 02481
Price
$55 / attendee
Welcome to New England's premier Cybersecurity conference.
Hosted by Towerwall and MassBay Community College
Please plan to join us for our 10th Annual Information Security Summit, New England’s leading cybersecurity conference and training event. Attendees come from nationwide to learn the latest developments and trends in information security.
This year’s premier cybersecurity Summit will present the latest threats and emerging technologies. Join other top security and risk management professionals for this special forum designed to expand your networking circles, inform you on the latest threats and trends and collaborate with the leading industry experts.
Attendees will earn up to 6 CPE credits.
Featured Speakers

David Sherry, MBA, CISSP ,CISM
Chief Information Security Officer,
Princeton University
Keynote Speaker

Michelle Drolet
Founder & CEO
Towerwall
Panel Moderator

Micheal Lyons
Chief Information Officer,
MassBay Community College
Panelist

Michael Sundberg
Senior Vice President, IT Security Director,
Middlesex Savings Bank
Panelist

Michelle A. Lord, ARM, CIC
Senior Vice President, Eastern Insurance
Panelist

Bob Turner
CISO for Education,
Fortinet
Panelist

Scott Tingley
Director, Security Architecture & Risk,
IntelyCare
Panelist

Michael Mimo
Chief Security Officer,
Copyright Clearance Center Inc.
Panelist

Greg Neville
CISO,
IntelyCare
Panelist

Keavy Murphy
Senior Director of Security,
Starburst Data
Panelist

Tamer Baker
Chief Technology Officer, Zscaler
& More...



Sponsors
The Information Security Summit 2023 is brought to you by:


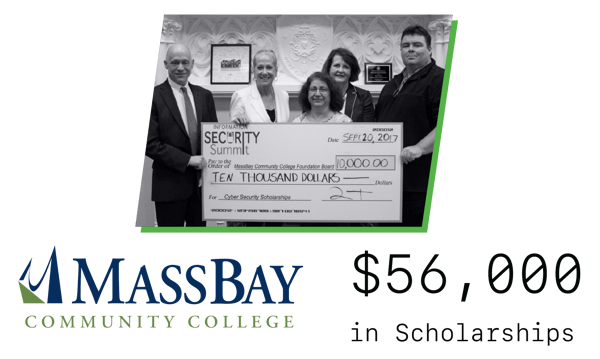
Supporting the Next Generation of InfoSec Leaders
MassBay Student Scholarship Fund
Funds raised during our Cybersecurity Executive Sessions will go to support the MassBay Student Scholarship Fund.
Each year, during our summit, we donate a MassBay Scholarship to support students with an interest in Information Security.
Since our inception 10 years ago, we have donated over $56,000 to the MassBay student scholarships to support the next generation of information security leaders.
If you would like to donate and support the fund, please follow the link below and select one of the 2 following options:
- Information Security Summit Certificate Scholarship Fulltime
- Information Security Summit Certificate Scholarship Parttime
Cybersecurity Organizations
The following organizations support and will attend the summit: